Is your store’s newsletter being used for phishing?
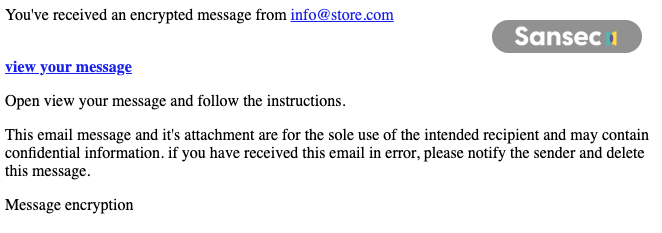
Cybercriminals in eCommerce are diversifying their targets, now aiming at entire customer databases instead of just stealing credit cards. A recent incident revealed this trend: a hacked Magento admin account was exploited to launch a phishing campaign through the platform's newsletter system, reaching all registered customers.
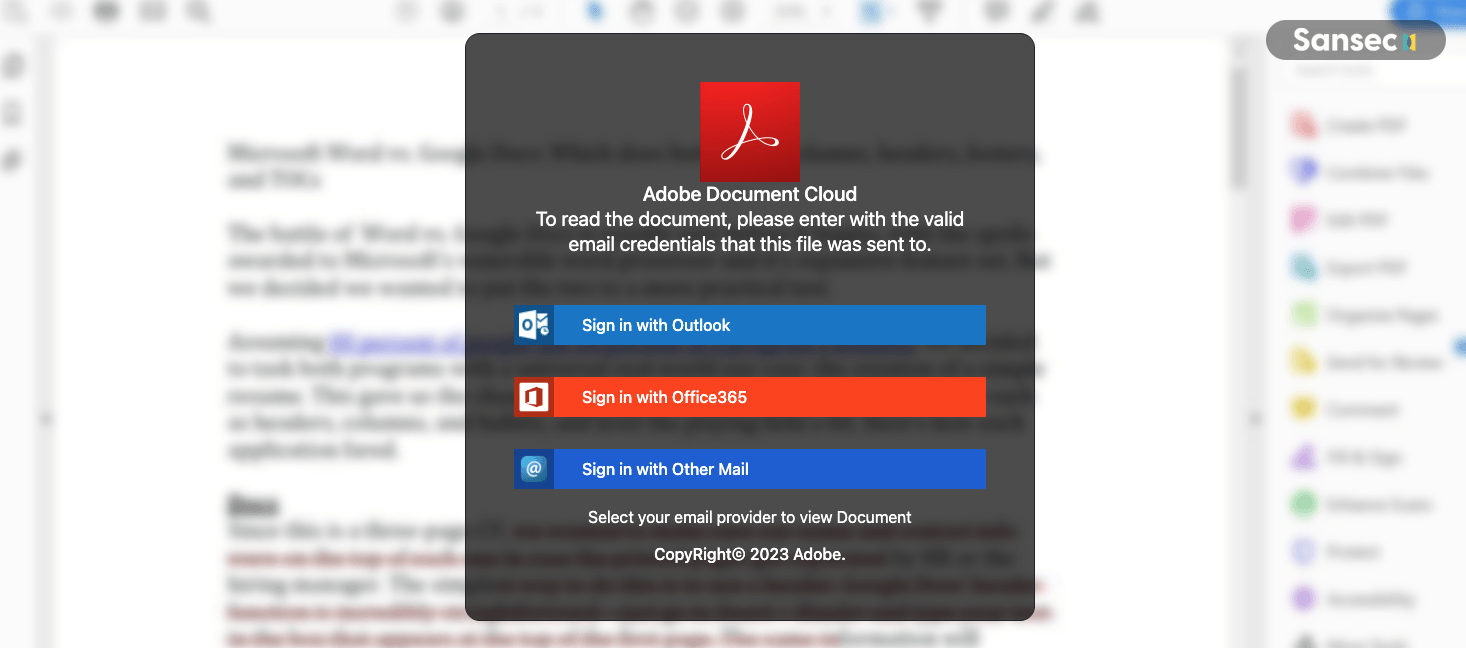
The phishing site, hosted on Cloudflare R2 (https://pub-7f69134e44ab4a03bb5e13c4894ffb4f.r2.dev/file.html), is designed to harvest passwords. Phishing is typically a high-risk, high-reward activity for cybercriminals, often leading to rapid detection. Interestingly, in this case, the attackers preferred phishing to the usual payment skimming methods. This shift could be due to the increasing effectiveness of multi-factor authentication in Europe, which diminishes the value of stolen payment card data.
This change in tactics shows that even online stores with secure, outsourced payment processes are not immune to cyber threats.
We have updated our eComscan detection heuristics to cover this attack vector, which is instantly available to all Sansec customers.
Thanks to our partner Savvii for their diligent investigation and professional followup.
Read more
Protect your store now!
Block all known Magento attacks, while you schedule the latest critical patch until a convenient moment. No more downtime and instability from rushed patching.
Get Sansec ShieldScan your store now
for malware & vulnerabilities
eComscan is the most thorough security scanner for Magento, Adobe Commerce, Shopware, WooCommerce and many more.
Learn more
