Sansec eComscan
saves you
time and money
With eComscan, eCommerce stores save 8 to 20 hours during the critical incident response stage of a hack.
Use eComscan
Your company is under attack. Customers have reported blocked credit cards. Google has blocked your advertisements. You have found suspicious code in the checkout. What else has been tampered with? And how did they get in?
Use our flagship product eComscan to quickly examine a store for malware, vulnerabilities, and unauthorized accounts. eComscan supports all popular platforms (like Magento) and will scan files, databases, and 3rd party components. On average, eComscan saves a technical team 8 to 20 hours of work during the critical incident response stage.
Pricing & specsHow does it work?
eComscan is fed 24/7 with threat intelligence from multiple sources. Because our research focuses exclusively on eCommerce fraud, we are usually weeks ahead in detecting the latest attack vectors.

Features include
Powerful threat intelligence
Our research team analyses 200 to 300 eCommerce hacks per week. This produces a valuable stream of attack vectors and IOCs, which is continuously fed into eComscan.
47% of our threat intel has not been discovered by other security firms, which is why many forensic investigators use our data.
Server-side monitoring
Merchants use eComscan to monitor their full store surface: from files & database triggers to rogue admin accounts and platform components.
Flexible reporting & integration
eComscan can alert you via multiple channels and formats. Email, Slack, phone, CSV, JSON. Integration with your existing monitoring solution is a breeze.
Vulnerability tracking & detection
A popular eCommerce attack vector are 3rd party extensions, which are costly to keep up to date. eComscan will alert you to those with 0day bugs. Discover weak spots in your defense, before others do.
eComscan reporting
Typically, eComscan is run in monitoring mode and will only alert you to relevant changes. When issues are found, it will log relevant meta data such as modification timestamps. And provide you with next-step instructions. See a sample report here.
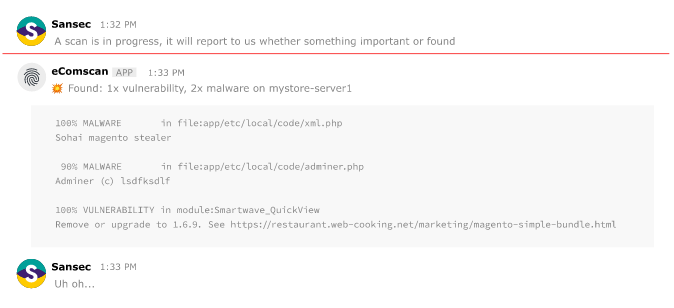
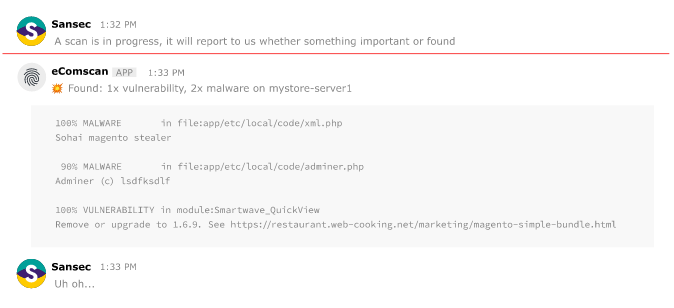
Activate your team via Slack
As most technical workflow is heavily integrated with Slack, you can easily hook eComscan up to your dev Slack channel and alert the right people without delay.
How Sansec eComscan tracks latest threats
Forensic analysis
Our experts are often “first at the scene”, hired by high profile victims for digital forensics and incident response. This uncovers new methodologies and fraud networks on a weekly basis. Our investigators were the first to publish about eCommerce skimming back in 2015.
Static Analysis
More than two hundred thousands stores are analyzed for malicious content and activity around the clock. This produces valuable insight in new threats.
Honeypot network
We run a network of honeypot (“bait”) webshops that produce valuable insight in the attacker TTPs (tactics, techniques and procedures). The latest signatures are distributed in real time to all of our clients.
Behavioral analysis
We work with ISPs, banks, Magento agencies and law enforcement to quickly disseminate attack methods when they are first spotted.
Security community
We receive many (anonymous) tips from fellow security companies or developers.
Historical analysis
We crawl and store historical copies of stores around the world. The data is then used for delta analysis to identify suspicious additions.
Extensions
Our open source initiative MageVulnDB is the authoritative source on third party vulnerabilities in Magento extensions. Developers and merchants across the globe maintain this database, which registers whether a Magento extension is safe to use.
Heuristic engine
Automated behavioral analysis of stores (“simulating real customers”) often yields new attack methods.
