Magento security extentions vendor got hacked

The store of a US Magento extension vendor was found compromised. Attackers had write access to the server selling extensions. We are awaiting a statement on the integrity of downloaded software.
Our malware crawlers detected a compromise of Extendware, a vendor of Magento extensions such as "Two-Factor Authentication". Attackers injected a payment skimmer on Oct 4th, as shown by this addition to the source code:
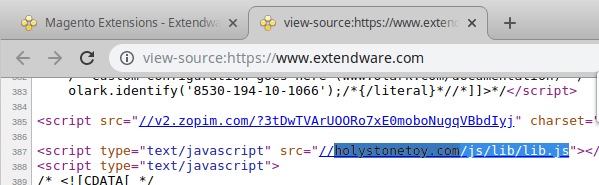
The actual skimmer can be found in this capture, which is a fairly standard keylogger. It sends customer card data to holystonetoy.com which is likely another compromised store under control of the attacker.
While our crawlers discover 50+ skimmers on a daily basis, this case stands out. First, the presence of malware proves that attackers had write access to Extendware's server. In theory, they could have injected a backdoor or skimmer in all of the Extendware products, thereby gaining control of all stores that would install their software. This is also known as a "supply chain attack".
Second, because e-commerce vendors are such an attractive target to payment skimmers, this Extendware case suggests that attackers may have used a novel method to gain access.
We have reported this breach to Extendware and asked about the integrity of their products but haven't heard back yet. Meanwhile, we recommend merchants who downloaded Extendware products in the last week to not install them and await further instructions from the vendor.
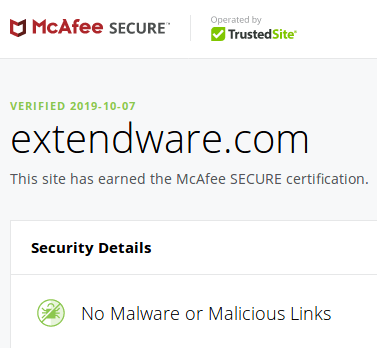
NB. Extendware runs a McAfee Secure seal which does not detect the compromise yet:
Read more
Protect your store now!
Block all known Magento attacks, while you schedule the latest critical patch until a convenient moment. No more downtime and instability from rushed patching.
Get Sansec ShieldScan your store now
for malware & vulnerabilities
eComscan is the most thorough security scanner for Magento, Adobe Commerce, Shopware, WooCommerce and many more.
Learn more
