Magento Developers Impersonated in Targeted GitHub Malware Operation
Criminals are targeting Magento developers with fake GitHub repositories that deliver RAT and keylogger malware to Windows users.
Rob Aimes alerted us to malicious GitHub repositories targeting Magento developers. The repos pose as legitimate tools but deliver Windows malware: a RAT and keylogger bundled as a LuaJIT package. The campaign is part of the FakeGit operation.
How the attack works
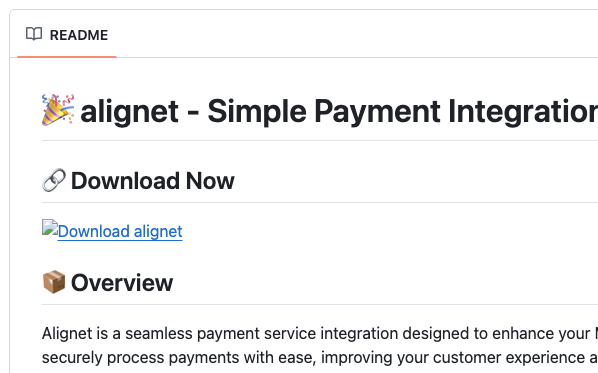
The attackers create repositories with luring names: deployment tools, Docker images, and configuration utilities. To appear trustworthy, they copy code from real open source projects, preserving the original commit history. This causes legit authors' avatars to appear in the "Contributors" section.
All repositories were created within the past 24 hours, though their commit timestamps appear older. These timestamps are fabricated.
By reusing commits from legitimate projects, the attackers make real open source contributors appear in the repository sidebar:
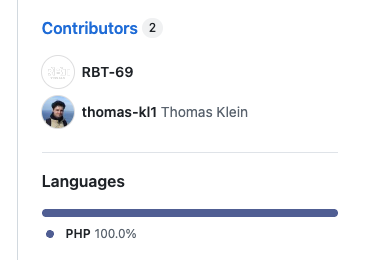
The publishing accounts share a distinctive activity pattern: dormant for months, then suddenly active:
Malicious repositories
Sansec identified these malicious GitHub accounts and repositories:
github.com/Uros5294/magento2-static-deploygithub.com/RBT-69/magento2-applicationgithub.com/suhanimish12/magento-frankenphp-imagesgithub.com/saddam237262/configdiffgithub.com/Sultanzacki9506/Google_Managergithub.com/NobreTakeshi/claude-code-magento-agentsgithub.com/ske1et2/Telegrams-Best-Scrappergithub.com/priya77771/module-widgetkit
| Repository | Original Author | Most Recent Committer Email |
|---|---|---|
| Uros5294/magento2-static-deploy | peterjaap (peterjaap@elgentos.nl) | |
| 61800321+Uros5294@users.noreply.github.com | ||
| RBT-69/magento2-application | Thomas Klein (thomasklein876@gmail.com) | tirouvingadamebaala@gmail.com |
| suhanimish12/magento-frankenphp-images | Mohamed El Mrabet (mimou78@gmail.com) | suhani.tfa@gmail.com |
| saddam237262/configdiff | Paul Frederiksen (paul@paulfrederiksen.com) | |
| 145244102+saddam237262@users.noreply.github.com | ||
| Sultanzacki9506/Google_Manager | Sultanzacki9506 (sultanzacky0@gmail.com) | sultanzacky0@gmail.com |
| NobreTakeshi/claude-code-magento-agents | NobreTakeshi (anime9x72@gmail.com) | anime9x72@gmail.com |
| ske1et2/Telegrams-Best-Scrapper | SkillSany (ClementinaBaptise59@hotmail.com) | osman.zhazaev12@gmail.com |
Payload analysis
Visitors are encouraged to download a ZIP file containing the "application." Inside is a self-contained LuaJIT runtime with an obfuscated Lua script. The package structure follows a consistent pattern across all repositories:
Launcher.bat (or Launcher.cmd)
lua51.dll
luajit.exe
[payload].txt # obfuscated Lua script (clx.txt, clib.txt, arch.txt, tcp.log)
The Lua script, when executed via the batch launcher, deploys a RAT and keylogger targeting Windows systems.
Indicators of Compromise
File hashes (SHA1)
The LuaJIT runtime is identical across all samples:
| File | SHA1 |
|---|---|
lua51.dll | 270f66d2c84ee86ff4b07c6220c51abd4897b5f0 |
luajit.exe | f5199b4191add11d02d58f521cbea21465b7ff6b |
Launcher scripts and obfuscated payloads vary per repository:
7adf9cf2b2cc720aa6ba45ef1be6e423e9576fed Manager_Google_1.0/Launcher.bat
6911c27ebedcad66076a8abf3c2d182ccf559feb Manager_Google_1.0/clx.txt
270f66d2c84ee86ff4b07c6220c51abd4897b5f0 Manager_Google_1.0/lua51.dll
f5199b4191add11d02d58f521cbea21465b7ff6b Manager_Google_1.0/luajit.exe
7adf9cf2b2cc720aa6ba45ef1be6e423e9576fed Software_2.5-beta.5/Launcher.bat
a72a4990db017897d37759f991e1c1515171c77b Software_2.5-beta.5/clx.txt
270f66d2c84ee86ff4b07c6220c51abd4897b5f0 Software_2.5-beta.5/lua51.dll
f5199b4191add11d02d58f521cbea21465b7ff6b Software_2.5-beta.5/luajit.exe
29ee31ee046198594bb712d186a14a49d1346a50 claude-code-magento-agents/Launcher.cmd
270f66d2c84ee86ff4b07c6220c51abd4897b5f0 claude-code-magento-agents/lua51.dll
f5199b4191add11d02d58f521cbea21465b7ff6b claude-code-magento-agents/luajit.exe
239087899df69b7ef9ba5d9716e3312c73c800ba claude-code-magento-agents/tcp.log
a6de13e6a4aef51f7b2bc298181ee5e02dd94861 magento-frankenphp-images_2.4/Launcher.cmd
bef485d8b3ab03ec389b984a231369f9aa2852c0 magento-frankenphp-images_2.4/clib.txt
270f66d2c84ee86ff4b07c6220c51abd4897b5f0 magento-frankenphp-images_2.4/lua51.dll
f5199b4191add11d02d58f521cbea21465b7ff6b magento-frankenphp-images_2.4/luajit.exe
df37352a15f99cb79f88d412bf20b145f83cbd12 static_deploy_magento_v1.9/Launcher.cmd
c6c9d7de860a848e4053acca3993d2d914889e64 static_deploy_magento_v1.9/arch.txt
Malicious GitHub accounts
Uros5294RBT-69suhanimish12saddam237262Sultanzacki9506NobreTakeshiske1et2
Recommendations
- Verify repository authenticity: check the account age, activity history, and whether the repository is linked from official project documentation
- Never run downloaded executables from untrusted sources, especially batch files that launch interpreters
- Report suspicious repositories to GitHub via their abuse reporting system
- If you downloaded and executed any of these packages, scan your system for malware immediately
For Magento store owners, run eComscan to detect any compromise on your server infrastructure.
You can monitor for new malicious repositories via GitHub's search, sorted by most recently updated.
Read more
In this article
Protect your store now!
Block all known Magento attacks, while you schedule the latest critical patch until a convenient moment. No more downtime and instability from rushed patching.
Get Sansec ShieldScan your store now
for malware & vulnerabilities
eComscan is the most thorough security scanner for Magento, Adobe Commerce, Shopware, WooCommerce and many more.
Learn more
