Credit cards of Atlanta Hawks fans stolen
Online credit card thieves - also known as Magecart - have managed to inject a payment skimmer in the online store of the Atlanta Hawks. Fans who ordered merchandize on or after April 20th had their name, address and credit card stolen.

Atlanta Hawks Shop
MageCart attacks on online stores surged last year, culminating in the hack of British Airways and Ticketmaster. This year the trend continues with another high-profile target. The Atlanta Hawks shop, claiming 7 million hits per year, was found leaking credit cards.
Analysis
On April 20th, our global Magecart Detection Network identified suspicious code on the checkout page of the Hawks store, as can be manually verified by viewing the page source:
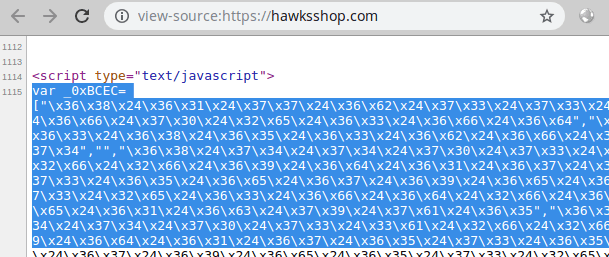
The gibberish code already bears the signature of Magecart, but to be sure, we render it into a readable copy. And indeed, it intercepts keystrokes as they are entered in the payment form. This activity can be observed when making a test purchase. Using Chrome Developer Tools, we see that during checkout, an extra request is made to the domain imagesengines.com:
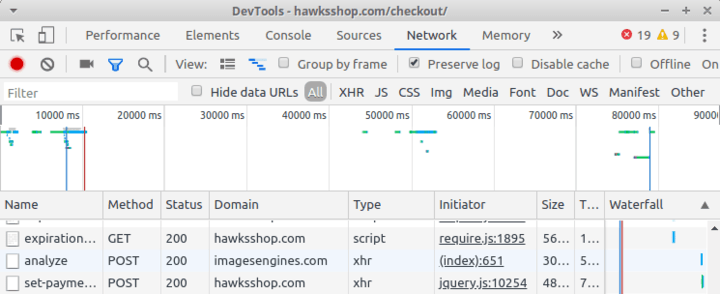
The payload is, as expected, the (encoded) name, address and card of our "bait shopper".
The exfiltration domain imagesengines.com has only been registered on March 25th and has nothing to do with the legitimate store. It is hosted with Leaseweb, a popular ISP among criminal actors.
How did attackers gain access
The Atlanta Hawks shop runs Magento Commerce Cloud 2.2, an enterprise-grade ecommerce system owned by Adobe. While Magento itself is quite secure, attackers often use insecure third-party components to gain access to the core of the shop system. Our previous research has uncovered a range of popular vectors: database management tools, marketing plugins and connected accounting software are in the top-3.
Read more
In this article
Protect your store now!
Block all known Magento attacks, while you schedule the latest critical patch until a convenient moment. No more downtime and instability from rushed patching.
Get Sansec ShieldScan your store now
for malware & vulnerabilities
eComscan is the most thorough security scanner for Magento, Adobe Commerce, Shopware, WooCommerce and many more.
Learn more
