PHP tool 'Adminer' leaks passwords

Adminer up to 4.6.2 found vulnerable, all should upgrade to 4.7.0
Update 2019-01-20: the root cause is a protocol flaw in MySQL.
Adminer is a popular PHP tool to administer MySQL and PostgreSQL databases. However, it can be lured to disclose arbitrary files. Attackers can abuse that to fetch passwords for popular apps such as Magento and Wordpress, and gain control of a site's database.
Exploitation happens in three stages. First, the attacker needs a modified MySQL server, which is altered to send out data import requests to any client that connects.
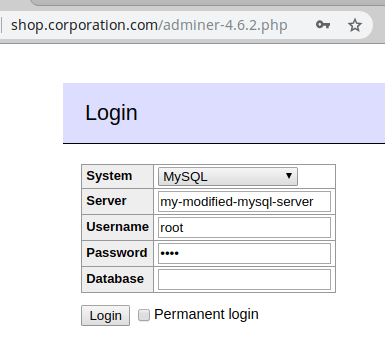
Second, an attacker needs to find an open adminer.php on the victim system. That is not hard, as many people install it in the root of their site. Once found, the attacker can instruct Adminer to connect to his rigged MySQL server (external connections are actually a feature of Adminer):
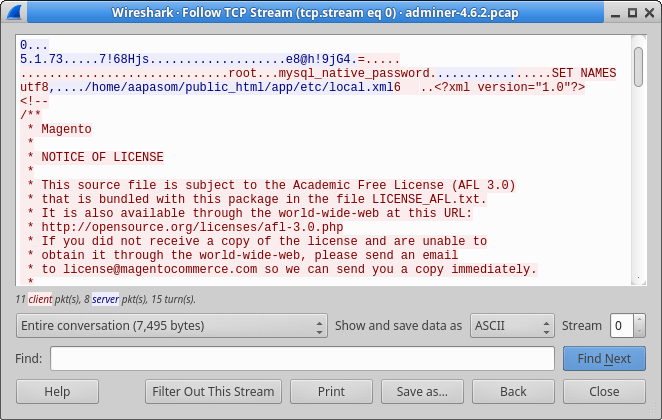
Adminer will then connect to the foreign server, login with the credentials, and immediately receive a data import request from the server for a specific file. Here is an example session, where Adminer sends the contents of local.xml (where Magento stores it secret database password) to the attacker-controlled server.
Third stage: as the attacker now has the master password for the victim site, he can use the same Adminer to access the database of the victim. And continue to steal private data or inject a skimmer.
Abuse in the wild
Until now there is no documented abuse of this method, but in hindsight we had observed it being used by different Magecart factions at least since October 2018 (although we didn't understand what was going on back then). The vulnerability was subsequently used to inject payment skimmers on several high-profile stores (government & multinationals).
Because different Magecart factions use it, we suspect that the modified MySQL server is for sale on the dark web.
Via our honeypots and customers Sansec has observed a recent surge in the volume of open Adminer scans. We expect that anyone running an unfixed Adminer will be breached in the coming months.
The fix?
We have tested Adminer versions 4.3.1 up to 4.6.2 and found all to be vulnerable. Adminer 4.6.3 was released in June, 2018 and appears safe. It is unclear whether the security flaw was fixed deliberately or by accident, as Adminer does not mention a security release.
We recommend anyone running Adminer to upgrade to the latest version (4.7.0). Also, we urge anyone to protect their database tools via an additional password and/or IP filter. Sometimes perpetrators can obtain your database password by other means, and an open Adminer makes life very easy for them.
Read more
In this article
Protect your store now!
Block all known Magento attacks, while you schedule the latest critical patch until a convenient moment. No more downtime and instability from rushed patching.
Get Sansec ShieldScan your store now
for malware & vulnerabilities
eComscan is the most thorough security scanner for Magento, Adobe Commerce, Shopware, WooCommerce and many more.
Learn more
